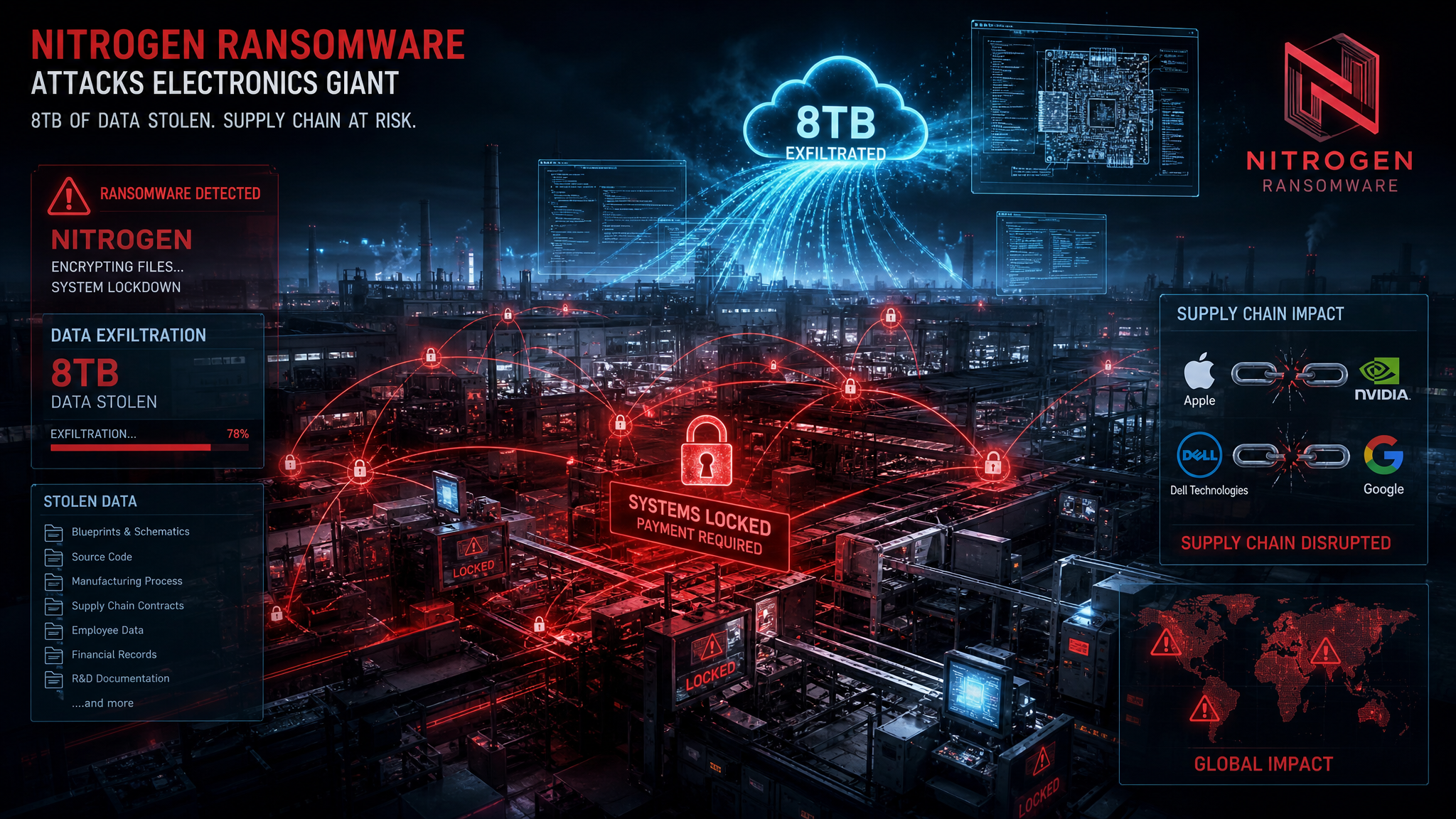
Foxconn confirmed on May 12, 2026, that its North American factories had suffered a major cyberattack. The Nitrogen ransomware gang had already listed the electronics manufacturing giant on its data leak site, claiming to have stolen 8 terabytes of sensitive data - over 11 million files - including confidential technical schematics and project details from some of the world's most valuable companies.
The victim list reads like a who's who of global technology: Apple, Nvidia, Dell, and Google are all reportedly affected. For an industry already reeling from the Canvas breach that shut down thousands of schools just days earlier, this attack confirms a disturbing trend. Ransomware groups have figured out that the fastest path to a massive payday runs straight through the manufacturing supply chain.
What Happened and When
The timeline unfolded with alarming speed. On Monday, May 11, 2026, the Nitrogen ransomware group posted Foxconn to its breach site alongside samples of stolen data. By Tuesday, Foxconn publicly confirmed that "some of its North American factories suffered a cyberattack" and that affected facilities were working to resume normal production.
Key Stat: The Nitrogen gang claims to have exfiltrated 8TB of data containing over 11 million files, including what they describe as confidential project files from major technology customers.
Foxconn's Mount Pleasant, Wisconsin facility was specifically identified as impacted. Production lines experienced disruptions but are gradually returning to normal. The company has not disclosed whether it paid a ransom, but the confirmation itself signals the severity of the incident.
Why Foxconn Is the Perfect Ransomware Target
Foxconn represents an almost ideal target for ransomware operators. As the world's largest electronics manufacturer, it holds not just its own intellectual property but the crown jewels of its customers. When you attack Foxconn, you are not just attacking one company. You are attacking the supply chain of the entire technology sector.
Allan Liska, a threat intelligence analyst at Recorded Future, put it plainly: "Ransomware groups are increasingly targeting victims that can impact the supply chain, whether it is physical or software. So it is unsurprising that a company like Foxconn would be targeted, since it does manufacturing and holds sensitive data for so many companies around the world."
Pro Tip: If your organization relies on contract manufacturers or supply chain partners, treat their security posture as an extension of your own. A breach at a partner is a breach at your perimeter.
Who Is the Nitrogen Ransomware Group
Nitrogen is not a household name in ransomware, but that makes them no less dangerous. The group emerged in 2023 and has maintained steady activity with periodic spikes, including an aggressive campaign at the end of 2024.
Operational Profile
Nitrogen primarily targets organizations in North America and Western Europe. Their victimology focuses on manufacturing, technology, and retail sectors - industries where downtime is costly and data is valuable. Ian Gray, vice president of intelligence at Flashpoint, notes that "manufacturing is one of the most-targeted sectors for ransomware in general."
The group has documented connections to the notorious ALPHV/BlackCat ransomware operation, one of the most disruptive ransomware cartels in recent years. This affiliation suggests Nitrogen may have access to sophisticated tooling and infrastructure that smaller groups lack.
A Fatal Design Flaw
Nitrogen's ransomware program is built on repurposed "Conti 2" code, but researchers at Coveware discovered a critical design flaw in the group's encrypting mechanism. The flaw makes it impossible to decrypt data once encrypted - even if the attackers want to release a victim's systems.
This creates a perverse incentive structure. Victims who pay the ransom may still never recover their encrypted files. For Foxconn, this design flaw may have influenced their incident response strategy, potentially making data recovery and restoration from backups the only viable path forward.
Common Mistake: Many organizations assume that paying a ransom guarantees data recovery. With groups like Nitrogen, the ransomware itself may be broken. Your backup strategy is your only reliable recovery mechanism.
The Supply Chain Domino Effect
The Foxconn breach is not an isolated incident. It is the latest and largest example of a strategic shift in how ransomware operators choose their targets.
Manufacturing Under Siege
Ransomware groups have realized that manufacturing organizations present a unique combination of high value and high vulnerability. These companies operate complex industrial environments where downtime can cost millions per hour. They also maintain deep integration with customer systems, meaning a single breach can compromise multiple organizations simultaneously.
Foxconn's position as a contract manufacturer for Apple, Nvidia, Dell, and Google makes it a force multiplier for attackers. Stealing Foxconn's data is equivalent to stealing fragments of each customer's intellectual property.
The Canvas Precedent
Just one week before the Foxconn attack, the education technology firm Instructure shut down its Canvas platform after the ShinyHunters extortion group breached 275 million user records. The attack paralyzed thousands of schools during finals season, demonstrating how supply chain and platform providers can become single points of failure for massive user populations.
The back-to-back nature of these attacks sends a clear signal. Ransomware groups are actively targeting the infrastructure that supports entire industries, not just individual enterprises.
Historical Context: Foxconn Has Been Here Before
Foxconn is no stranger to ransomware. The company has faced multiple extortion attempts in recent years:
- December 2020: The DoppelPaymer group attacked a Mexican facility and demanded 1,804 bitcoin (roughly $34 million at the time)
- May 2022: The LockBit group hit another Mexican facility and disrupted production
- 2024: LockBit attacked subsidiary Foxsemicon Integrated Technology with defacements and data breach claims
This history raises uncomfortable questions about whether previous incidents led to meaningful security improvements. For an organization of Foxconn's scale and sensitivity, repeated victimization suggests systemic gaps in defensive posture.
What Was Stolen and Why It Matters
The Nitrogen gang claims their 8TB haul includes technical schematics and project details from major customers. If accurate, the implications extend far beyond Foxconn itself.
Intellectual Property at Risk
For companies like Apple and Nvidia, product schematics represent billions of dollars in research and development investment. Early access to design specifications could enable competitors to copy features, undermine market positioning, or identify vulnerabilities in upcoming products.
Key Stat: The global cost of intellectual property theft exceeds $600 billion annually, and manufacturing supply chain breaches are among the most efficient vectors for this type of exfiltration.
Competitive Intelligence Goldmine
Beyond direct IP theft, the stolen data likely contains pricing information, production timelines, supplier relationships, and quality metrics. This intelligence is invaluable to competitors and nation-state actors seeking to understand the strategic direction of the world's largest technology companies.
Regulatory and Legal Exposure
Foxconn's customers are subject to stringent data protection and supply chain security regulations. A breach at a contract manufacturer can trigger reporting obligations, regulatory investigations, and contractual liability that cascades through the entire supply chain.
What CISOs Must Do Now
The Foxconn breach is a wake-up call for any organization that relies on third-party manufacturing or supply chain partners. Here are the concrete actions security leaders should take immediately.
1. Audit Your Supply Chain Security Posture
If you have not conducted a comprehensive security assessment of your contract manufacturers and logistics partners in the past 12 months, schedule one now. The assessment should cover:
- Network segmentation and access controls
- Data handling and classification practices
- Incident response capabilities and notification procedures
- Backup and recovery testing frequency
- Third-party security certifications and attestations
Key Takeaway: Your security is only as strong as the weakest link in your supply chain. A $100 million security budget means nothing if your contract manufacturer runs on default passwords and unpatched systems.
2. Implement Supply Chain Threat Monitoring
Traditional security monitoring focuses on your own environment. Supply chain threat monitoring extends that visibility to your partners. Key capabilities include:
- Dark web monitoring for mentions of your partners or leaked data bearing your trademarks
- External attack surface monitoring for partner infrastructure
- Threat intelligence feeds focused on manufacturing and logistics sectors
- Automated alerting for ransomware group victim announcements
3. Demand Security Transparency
Your contracts with manufacturing partners should include explicit security requirements and audit rights. Minimum expectations should include:
- Annual third-party security assessments
- Mandatory incident notification within 24 hours of discovery
- Evidence of ransomware-specific defenses including offline backups
- Network segmentation that prevents lateral movement from partner to customer environments
4. Prepare for the Multi-Victim Breach
The Foxconn attack demonstrates that a single breach can affect multiple organizations simultaneously. Your incident response plan should account for:
- Coordinated response with affected partners and customers
- Legal and regulatory notification requirements across multiple jurisdictions
- Public communications strategy that addresses stakeholder concerns without amplifying attacker demands
- Forensic preservation requirements that may span multiple organizations
5. Test Your Recovery Assumptions
Nitrogen's broken encryption mechanism means that paying the ransom does not guarantee recovery. Your organization needs validated, tested recovery capabilities:
- Immutable backups that cannot be encrypted by ransomware
- Air-gapped recovery environments that are isolated from production networks
- Quarterly recovery drills that test full system restoration from backup
- Documented recovery runbooks that do not depend on internet access or compromised infrastructure
Pro Tip: If your disaster recovery plan assumes you can pay a ransom and get your data back, you do not have a recovery plan. You have a gambling strategy.
The Broader Implications for Manufacturing Security
The Foxconn breach signals a broader shift in how ransomware operators think about target selection. Here is what this means for the future.
Physical and Digital Convergence
Manufacturing is unique among ransomware targets because the impact spans both digital and physical domains. Encrypting a factory's systems does not just lock files - it stops production lines, halts shipments, and disrupts global supply chains. This dual impact makes manufacturing targets more lucrative and more disruptive.
The Platform Provider Problem
Companies like Foxconn and Instructure share a common characteristic. They are platform providers whose compromise affects thousands of downstream customers. Ransomware groups have identified this concentration risk and are actively exploiting it. Expect more attacks on manufacturing platforms, logistics providers, and shared service organizations.
Nation-State Interest
The intellectual property stolen in manufacturing breaches is not just valuable to criminals. It is valuable to nation-states seeking to accelerate their own technological development. The line between financially motivated ransomware and state-sponsored espionage is increasingly blurry, with some groups serving both masters.
What Happens Next
Foxconn's incident is still unfolding, but several near-term developments are likely.
Customer Notification Cascade
Apple, Nvidia, Dell, and Google will need to assess whether the stolen data contains information that triggers their own breach notification obligations. Depending on the nature of the exfiltrated files, this could lead to regulatory filings, customer notifications, and contractual disputes that extend far beyond Foxconn.
Ransom Negotiation or Public Leak
Nitrogen will likely attempt to negotiate a ransom payment. If Foxconn refuses or negotiations fail, the group may begin publishing stolen data to pressure payment. Given the broken encryption mechanism, data publication may be Nitrogen's only remaining leverage.
Security Investment Surge
Manufacturing organizations globally will likely accelerate security investments in response to this high-profile breach. Areas of increased focus will include network segmentation, endpoint detection and response, backup immutability, and supply chain security assessments.
Conclusion
The Foxconn ransomware attack is more than another entry in the growing list of 2026 breaches. It is a demonstration of how ransomware groups have evolved their targeting strategy to exploit the interconnected nature of global manufacturing. By attacking Foxconn, Nitrogen did not just compromise one company. They potentially compromised the intellectual property of the world's most valuable technology brands.
For CISOs and security leaders, the message is clear. Supply chain security is no longer a procurement checkbox or a compliance exercise. It is a core defensive requirement. The organizations that treat partner security as an extension of their own posture will weather these attacks. Those that assume their partners can fend for themselves will find their most sensitive data exposed through the weakest link in their chain.
The 8TB of stolen data represents more than files on a server. It represents the accumulated innovation of decades of research and development, now in the hands of criminals. Whether that data is ever published, sold, or weaponized remains to be seen. But the fact that it was stolen at all should be enough to prompt immediate action across every organization that relies on contract manufacturing.
Foxconn will recover. Production will resume. But the stolen data does not come back. And for Apple, Nvidia, Dell, and Google, that loss is permanent.
The supply chain is only as strong as its most vulnerable partner. Nitrogen just proved how devastating that vulnerability can be.